ICS Security – More Important Than Ever
In 2007, an experiment proved that hackers targeting electrical utility would have little trouble damaging critical elements of America’s power grid. Even though the experiment happened several years ago the outcomes are still relevant and relate to the ICS security work Secmation is currently undertaking. This happened about 10 years ago and has been known about inside cyber circles for some time.
In Andy Greenberg‘s story from Wired: How 30 Lines of Code Blew Up a 27-Ton Generator he discusses how Mike Assante’s 2007 experiment with Idaho National Labs to demonstrate the vulnerabilities of our power systems, resulted in lasting lessons. As Assante says:
“The implication was that with just a few lines of code, you can create conditions that were physically going to be very damaging to the machines we rely on.”
The exercise, referred to as the “Aurora experiment” was intended to demonstrate the vulnerability of America’s energy infrastructure to adversary threat. In 2021 the threat is just as real as it was in 2007.
The experiment resulted in the destruction of a large generator that Assante and his Idaho National Labs team bought and shipped from an Alaska Oil Field.
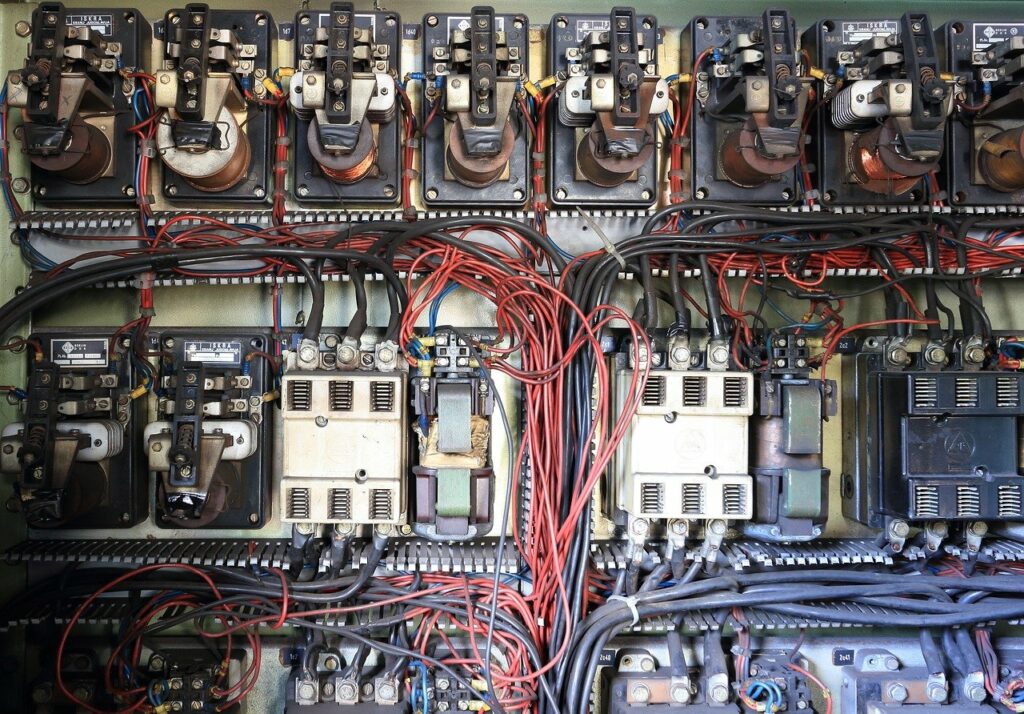
This demonstration highlights what a cyberattack can do to real industrial equipment. Secmation is actively working to defend industrial control systems from adversarial threat.
Partner With Us
Let’s connect on how Secmation can help you and your customers.